WordPress is one of the most popular content management systems used by millions of websites worldwide. However, recent reports have highlighted a critical vulnerability in Ultimate Member plugin, a popular user registration and login plugin for WordPress. This vulnerability poses a significant risk to over 200,000 WordPress websites.
The Ultimate Member plugin is designed to simplify user registration and login processes, offering various features such as user profiles, role definitions, custom form fields, and member directories. Unfortunately, this plugin has been targeted by attackers exploiting a critical vulnerability, tracked as CVE-2023-3460, which allows unauthorized users to add new accounts with administrator privileges.
Contents
Understanding the vulnerability and its impact
The CVE-2023-3460 vulnerability in the Ultimate Member plugin has a high CVSS score of 9.8, indicating its severity. Attackers have discovered a conflict between the plugin’s blocklist logic and how WordPress handles metadata keys. By exploiting this conflict, attackers can manipulate metadata keys, including the one responsible for storing user roles and capabilities. This manipulation enables them to create user accounts with administrator privileges without proper authorization.
Reports suggest that unauthorized accounts have been created since the beginning of June, indicating an ongoing attack. Although the maintainers of the Ultimate Member plugin have released two recent versions attempting to address the vulnerability, it appears that the patch has not fully resolved the issue. Therefore, it is crucial for WordPress site owners to take immediate action to protect their websites.
Steps to mitigate the risk
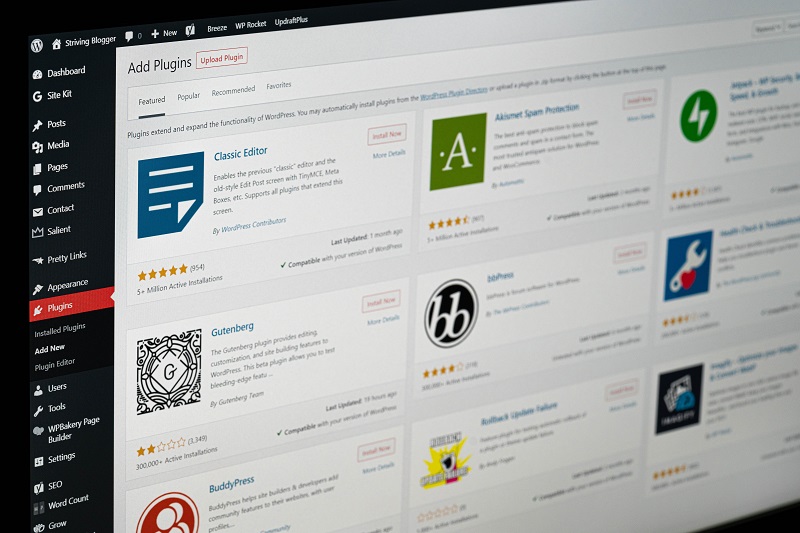
Step 1: Disable the Ultimate Member plugin
To mitigate the risk posed by the Ultimate Member plugin vulnerability, site owners are strongly advised to disable the plugin until an effective patch is available. By deactivating the plugin, potential attackers will be unable to exploit the vulnerability and gain unauthorized access to the website. Keep an eye on the official updates from the Ultimate Member plugin developers for information on when a secure version will be released.
Step 2: Conduct an audit of administrator roles
It is recommended to conduct an audit of administrator roles on affected websites. This audit helps identify any suspicious or rogue accounts that might have been created by attackers before the vulnerability was discovered. By reviewing the list of administrators, you can ensure that only authorized individuals have access to the backend of your WordPress site. Remove any unauthorized or suspicious accounts promptly to maintain the security and integrity of your website.
Securing your WordPress website is of utmost importance to protect your data and maintain the trust of your users. The ongoing attack targeting the Ultimate Member plugin vulnerability emphasizes the need for proactive measures. By disabling the plugin and conducting an audit of administrator roles, you can mitigate the risk and safeguard your website from unauthorized access.
Remember, staying updated with security patches and taking preventive actions will help you maintain a secure online presence and protect your valuable information.
Implement these steps today to fortify your WordPress website and stay one step ahead of potential threats.