Ukrainian authorities have issued a stern caution regarding a series of assaults directed at governmental bodies through the utilization of the ‘Merlin’ open-source post-exploitation toolkit. ‘Merlin’, crafted in the Go programming language, stands as a versatile toolkit accessible on GitHub, meticulously designed for red team operations within the realm of cybersecurity.
The toolkit, ‘Merlin’, encompasses a repertoire of functionalities encompassing diverse communication protocols, encryption methodologies, and execution tactics tailored for compromised networks. Regrettably, certain malicious entities are misusing the ‘Merlin’ toolkit, deploying it for unauthorized onslaughts, thereby proliferating across breached networks.
The Computer Emergency Response Team Ukraine (CERT-UA) has successfully identified these attacks, which frequently commence with malevolent phishing emails masquerading as legitimate communications from the agency itself. These deceptive emails bear attachments in the form of CHM files, which, when executed, trigger a sequence of JavaScript commands, ultimately leading to the deployment of the ‘ctlhost.exe’ executable.
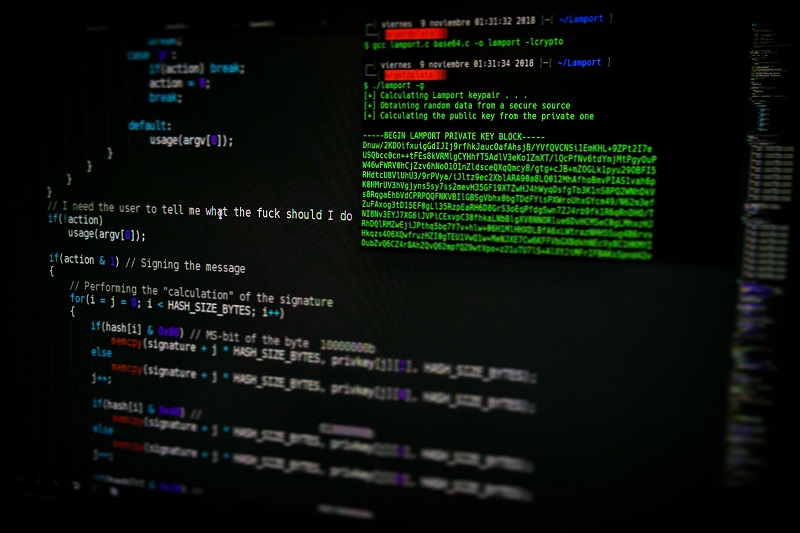
The execution of ‘ctlhost.exe’ inevitably culminates in the infection by the ‘MerlinAgent’, thereby granting malicious actors unwarranted entry to the victim’s machinery as well as the encompassing network environment. Designating this malicious endeavor with the designation ‘UAC-0154’, CERT-UA has documented the initial instances of these attacks as of July 10, 2023.
It is worth highlighting that the deployment of open-source tools like ‘Merlin’ perplexes the process of attribution, as it significantly diminishes the digital breadcrumbs that could be utilized to trace back to specific malefactors. Consequently, this serves as a resounding reminder of the pressing requirement for robust cybersecurity measures to be entrenched, safeguarding vital establishments against relentless attacks.
Adil Sattar is a seasoned writer, SEO expert, and technology journalist with years of hands-on experience in the digital content and IT industries. With a passion for uncovering the latest breakthroughs in technology, Adil has dedicated his career to making complex tech concepts simple, engaging, and accessible to a broad audience.
Armed with deep expertise in search engine optimization, Adil understands not just how to write great content — but how to make sure it reaches the right audience. His work spans a wide range of technology topics including artificial intelligence, cybersecurity, software development, consumer electronics, and digital innovation.
As the founder and lead writer at TechBeams, Adil has built a platform trusted by tech enthusiasts, IT professionals, and everyday readers alike. His unique blend of technical knowledge, SEO acumen, and storytelling ability sets TechBeams apart as a go-to destination for reliable and insightful tech content.
When he’s not writing or researching the next big thing in tech, Adil is constantly learning, adapting, and staying ahead of the curve in an ever-evolving digital landscape.



